Second DDoS attack against intelx.io
We were under a DDoS attack on January 26, 2020. We received 4,935,580 HTTP requests in 3 minutes from the 2 IPs 149.202.101.151 and 54.38.23.181. It was the second DDoS attack – the last one was on September 19, 2019.
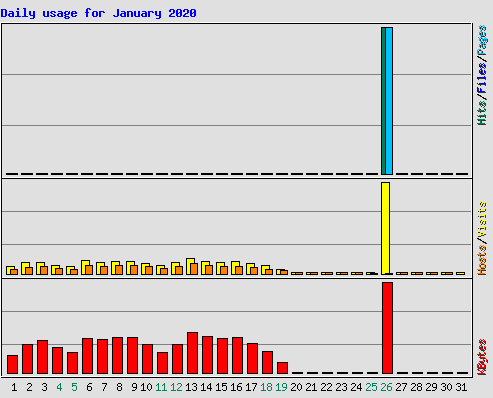
You can see the spike clearly in the monthly usage statistics below. The attack was not successful and was only discovered when creating monthly usage statistics.