North Korea just got a 3rd internet connection (and no one noticed)
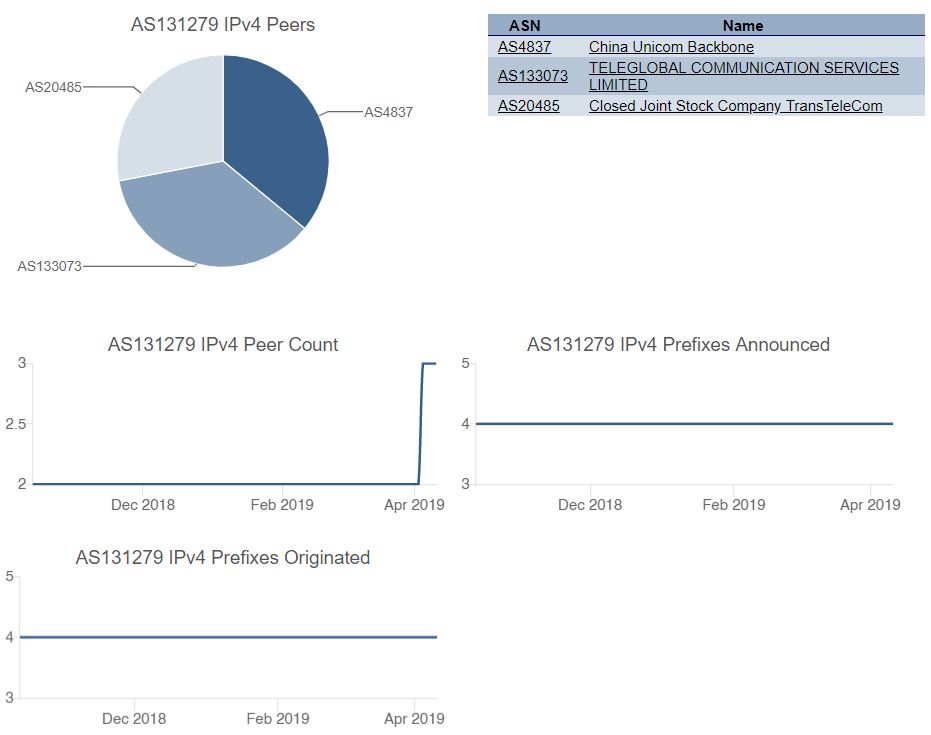
Say hello to North Korea’s 3rd internet uplink! The North Korean autonomous system AS131279 just got a new uplink to AS133073 Teleglobal Communication Services Limited – which is assigned to Hong Kong, according to APNIC. According to our information, it went live a few days ago on April 3, 2019 at 16:00 UTC.
North Korea currently has 2 existing uplinks, one via China (AS4837 China Unicom Backbone) and another via Russia (AS20485 Closed Joint Stock Company TransTeleCom). This third new uplink gives them more flexibility, redundancy, and resistance against attacks such as DDoS.
Where is this uplink physically connected? We don’t know and can only speculate (or ask Teleglobal). Just because the new uplink is registered to Hong Kong (in the who-is data), does not mean that the physical connection goes there; it is possible that the physical cable is placed somewhere near the Shenyang/Liaoning region.
What does this mean for the North Koreans? For those 0.1% (including foreigners) that have access to the internet, it most likely means better internet. More uplinks allows North Korea to handle more traffic and redirect traffic to different routes in case one fails.
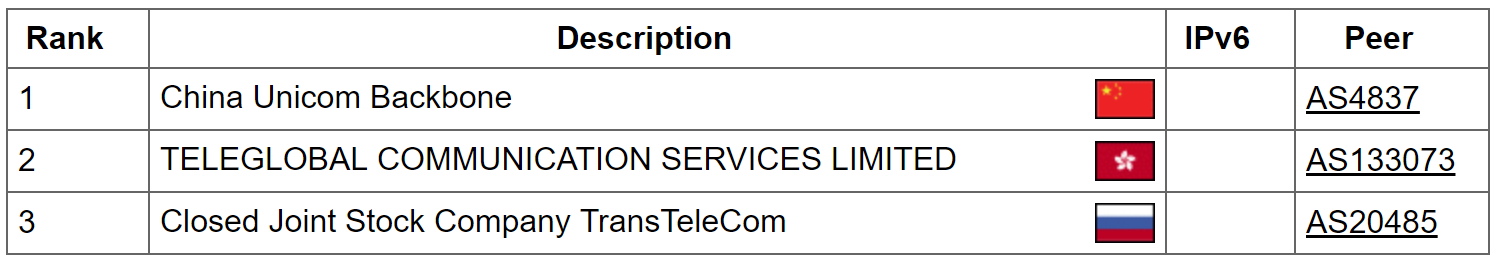
bgp.he.net/AS131279#_peers shows the 3 peers (uplinks):
Teleglobal
Teleglobal’s website is http://www.kf-idc.com/. Below is the who-is data of AS133073 which lists their contact information:
aut-num: AS133073
as-name: SZKF-AS-AP
descr: TELEGLOBAL COMMUNICATION SERVICES LIMITED
country: HK
org: ORG-TCSL1-AP
admin-c: TCSL1-AP
tech-c: TCSL1-AP
mnt-by: APNIC-HM
mnt-routes: MAINT-SZKF-HK
mnt-irt: IRT-SZKF-HK
last-modified: 2018-11-08T00:28:13Z
source: APNIC
irt: IRT-SZKF-HK
address: flat/rm 801 join-in Hang Sing Centre,, 2-16 Kwai Fung Crescent, Kwai Chung, NT.,, Hong Kong
e-mail: kwaifong33@gmail.com
abuse-mailbox: abuse@kf-idc.com
admin-c: TCSL1-AP
tech-c: TCSL1-AP
auth: # Filtered
mnt-by: MAINT-SZKF-HK
last-modified: 2014-05-05T11:49:50Z
source: APNIC
organisation: ORG-TCSL1-AP
org-name: TELEGLOBAL COMMUNICATION SERVICES LIMITED
country: HK
address: flat/rm 801 join-in Hang Sing Centre,
address: 2-16 Kwai Fung Crescent, Kwai Chung, NT.,
phone: +85231885386
e-mail: kwaifong33@gmail.com
mnt-ref: APNIC-HM
mnt-by: APNIC-HM
last-modified: 2017-08-29T23:21:20Z
source: APNIC
Existing Russian Uplink
The Russian uplink to AS20485 Closed Joint Stock Company TransTeleCom was created on October 1, 2017, according to this article:
https://dyn.com/blog/north-korea-gets-new-internet-link-via-russia/
Chinese Uplink
The North Korean AS131279 was created on December 21, 2009. The uplink to the Chinese AS4837 went live on September 17, 2010 at 08:00 UTC.