🐍 Python code to use Intelligence X
We just added Python code to use the Intelligence X API! You can find the code in the SDK at github.com/IntelligenceX/SDK.
The code comes with a default API key so you can get started right away. For details on usage please look at the readme file in the SDK.
The SDK already has code implementations in HTML, PHP, and Go. It also features a command-line program written in Go, and can be compiled on Windows/Linux/Mac. The Python reference implementation is the latest addition to help developers integrate our search engine and our special Phonebook feature.
Scripts included
There are 2 scripts included in the SDK:
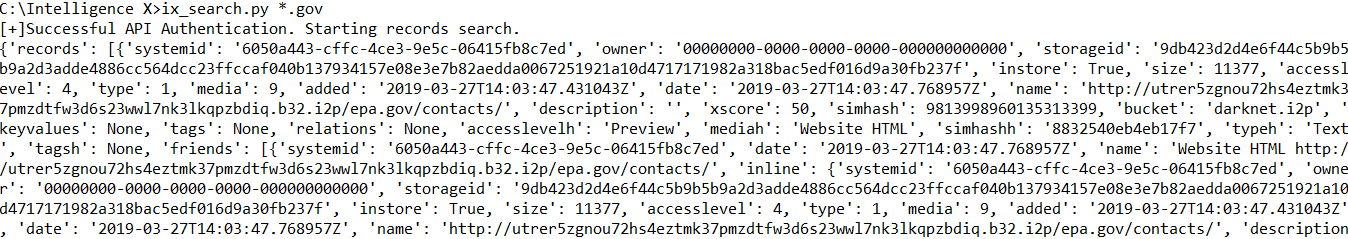
ix_search.py <selector>
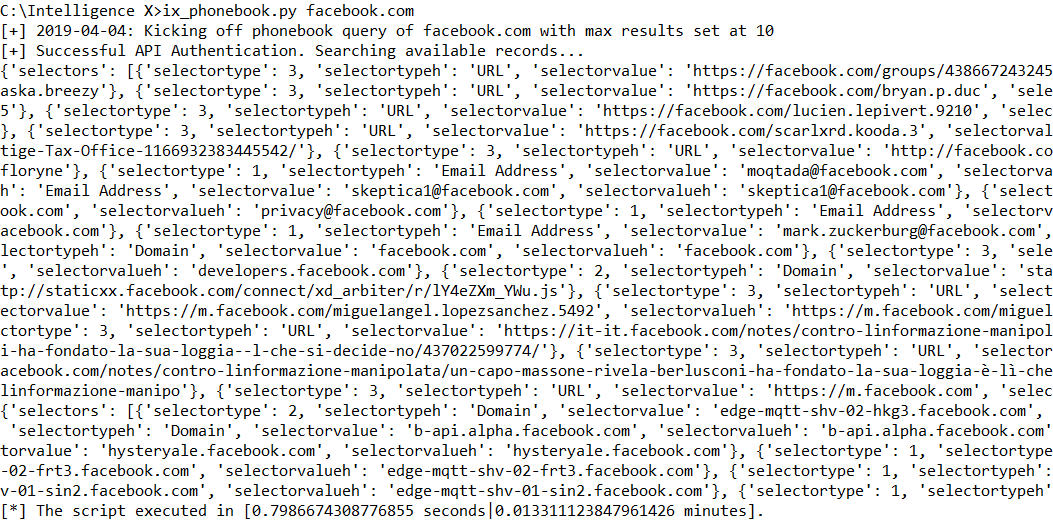
ix_phonebook.py <selector>
The first script “ix_search.py” looks for any selectors, and returns all results that contain the selector. Each result has a unique “systemid” that can be used to query the actual data (note that the source data could be anything from a HTML document, a text file, a Word document, a PDF, etc.).
The second script “ix_phonebook.py” makes a phonebook lookup, i.e. it lists all selectors known for the search term. In the example below, it lists known email addresses, URLs, and domains belonging to facebook.com.