New: Identity Portal 🎉
We launched a new product: “Identity Portal”! It allows users to find all lines in a text where a search term appears, and to download a list of leaked accounts under a specific domain or email address.
This product is exclusively available on request to companies and governments. If you are interested, please contact us!
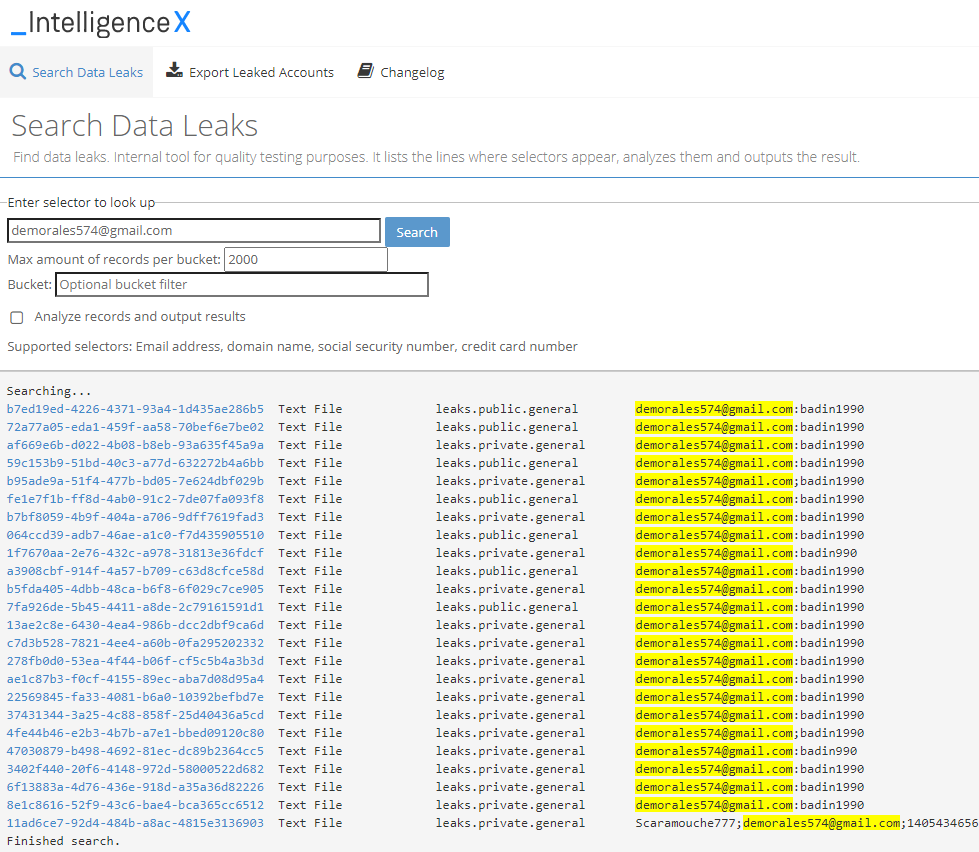
List all lines where the search term appears in the results
This function searches for and lists all lines where a search term appears, and like intelx.io, it searches across all data categories. Each line contains first the ID of the search result, which can be opened by clicking on it. The next columns show the file type and the data category, followed by the line where the search term appears.
This allows analysts to go over hundreds of results and quickly identify duplicates and relevant and irrelevant findings. The screenshots below show the lookup for Dmitry Badin, a supposed GRU member who allegedly hacked the German Bundestag.
List leaked accounts and export as CSV file
The second tab, “Export Leaked Accounts”, allows users to search for a domain or email and lists all potentially leaked accounts found for a target. It analyzes the password type, including the detection of various hashes, and provides information about the source.
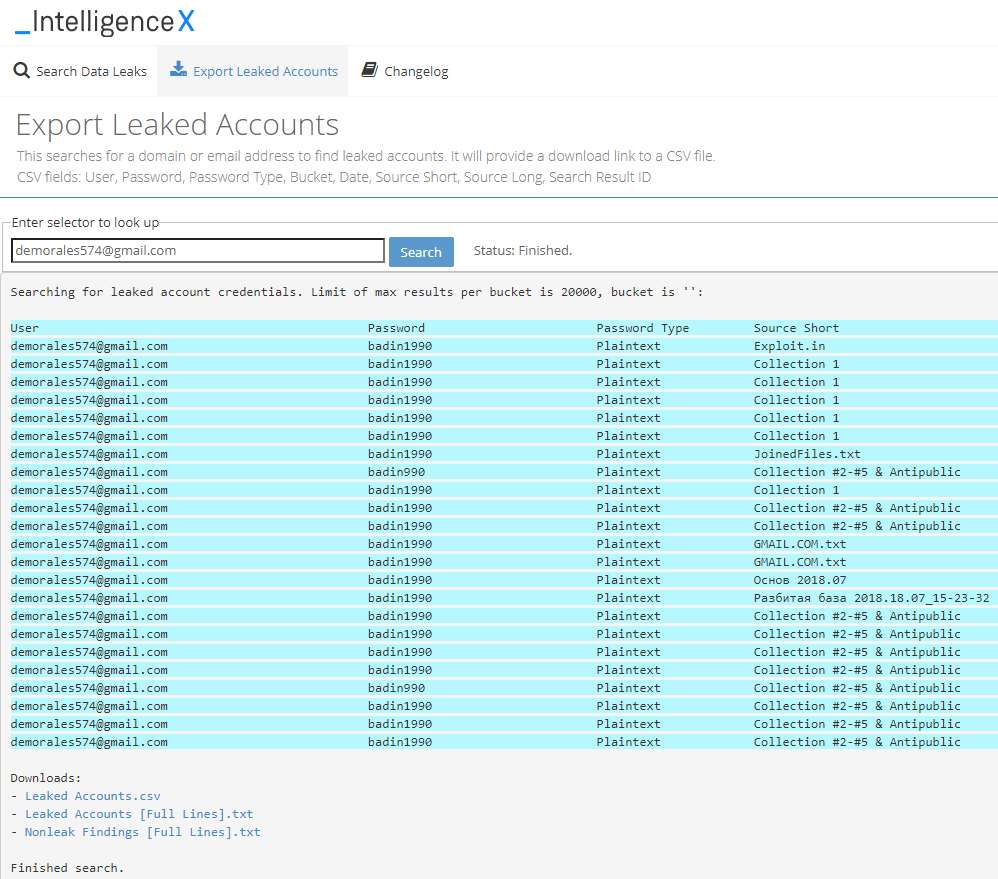
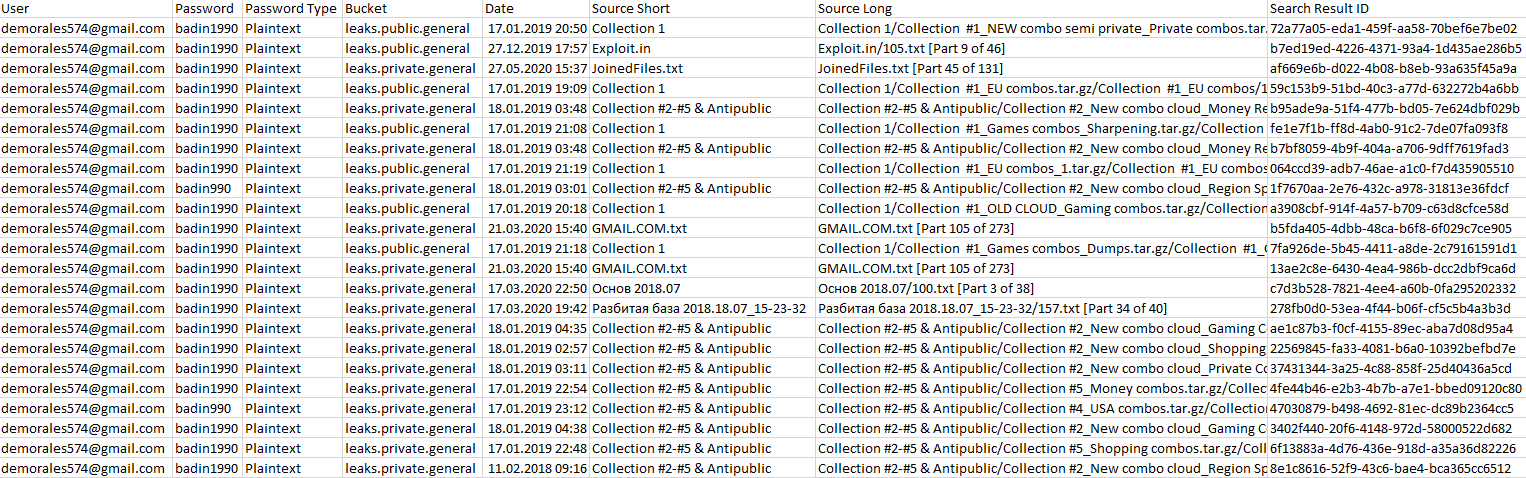
It provides a download link to a CSV file listing all the results. Example CSV file:
There is a lot of engineering behind both functions since it reads all search results data in real-time, converts them to text, and analyzes the result to determine whether it is a leaked account. Given that Intelligence X searches more than 20 billion records, this can result in Gigabytes of data being processed for a single request.