How many WiFi networks does North Korea have? At least 1.
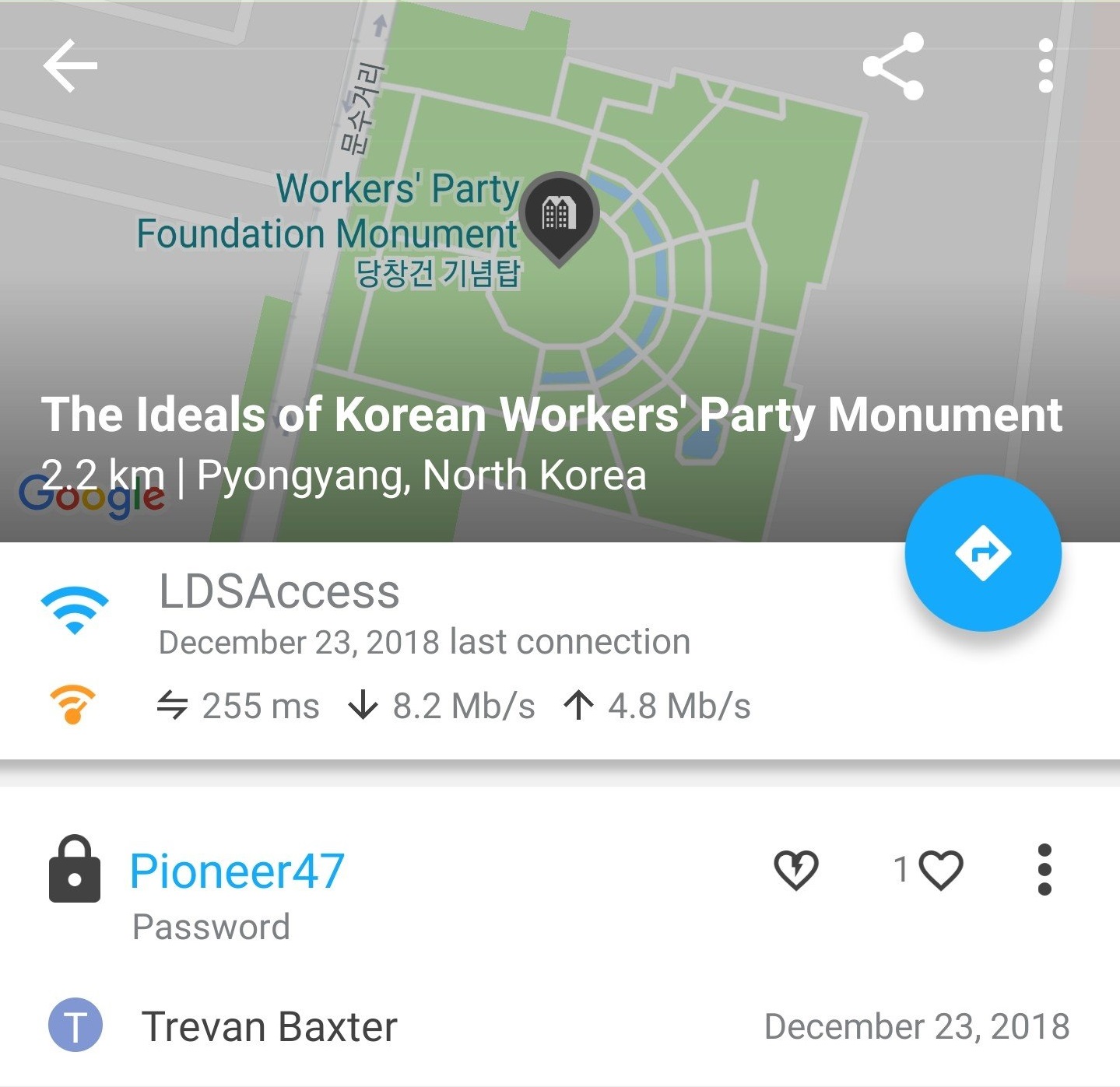
North Korea has at least 1 WiFi network! The above screenshot was taken from the app, WiFi Map, which shows WiFis added by users (crowd-sourced). In this case, user “Trevan Baxter” added a WiFi network on December 23, 2018. The app first connects to the WiFi before adding it to the database to make sure it really exists.
The screenshot shows that the WiFi with the access point name, “LDSAccess”, and password, “Pioneer47”, exists at the “Ideals of Korean Workers Party Monument” in Pyongyang, North Korea. The connection is acceptable with 8.2 MB/s down and 4.8 MB/s up, thus it allows you to watch Netflix in HD in Pyonyang (Netflix recommends 5 MB/s down). Multiple independent reports claim that the internet in North Korea is not filtered; indeed, you can watch Netflix on your next trip to Pyongyang.
It is worth noting that the WiFi name “LDSAccess” with the password “Pioneer47” is used as a default in LDS churches, aka, the Mormon Church. Why this would pop up in North Korea can only be speculated.
Confirmed Places with WiFi
WiFi hotspots aren’t new to Pyongyang, according to a report from nknews.org from 2015:
There are a number of Wi-Fi access points around Pyongyang which are exclusively for foreigners, […]
Only devices with foreigners-only SIM cards can access to Pyongyang’s Wi-Fi,” said Choi. “So ordinary citizens of Pyongyang can’t access it.”
The Pyongyang’s international airport was reported to have WiFi on December 23, 2017.

Internet corner in the departures lobby of Pyongyang’s international airport. Photo credit: AP
It was confirmed in 2018 that there is WiFi at the Pyongyang’s Potonggang Hotel (the article shows a picture of a Taiwanese “ZyXEL P-600” router).