NSA program FAIRVIEW: Collecting trash. 🗑️
Fairview is a NSA program designed to collect “phone, internet, and e-mail data mainly of foreign countries’ citizens at major cable landing stations and switching stations inside the United States”. It dates back to 1985 [1]. There are various good articles on the subject [2].
As with every mass surveillance program, the basic law of collection (and search queries) is:
Garbage in, garbage out.
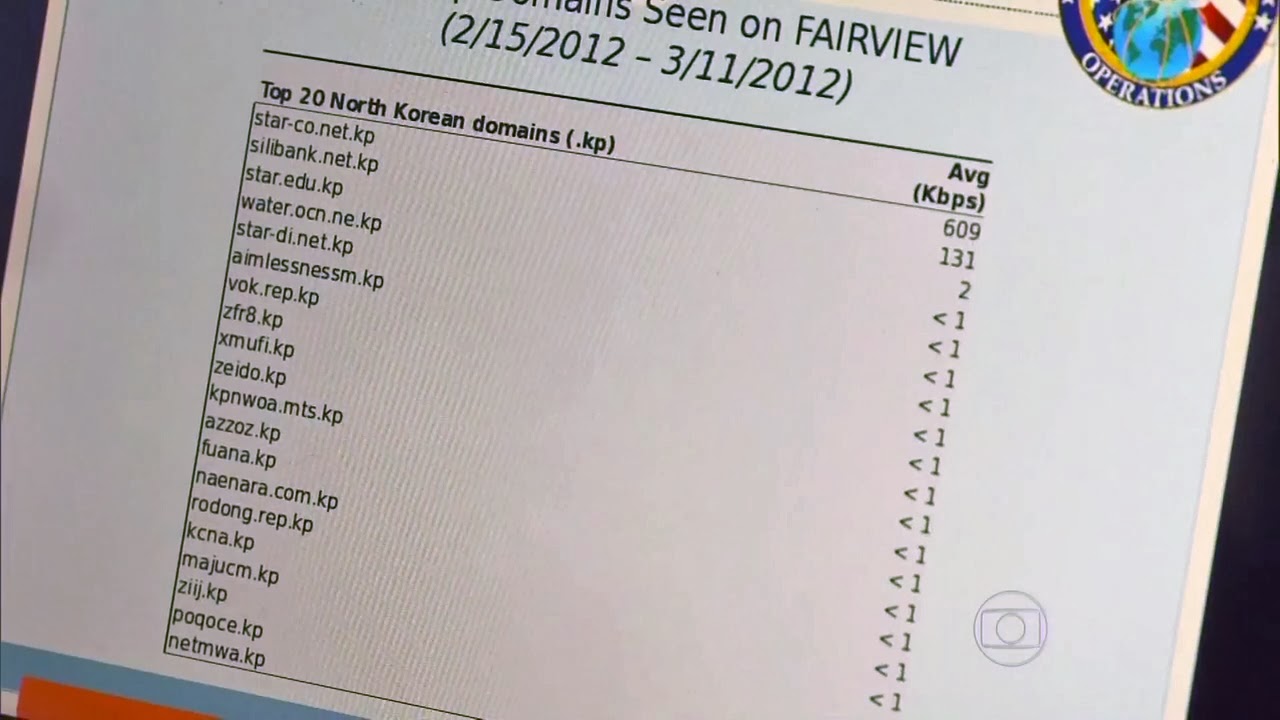
List of North Korean domains captured by FAIRVIEW. Picture Source
Since Intelligence X crawls North Korean domains (see our archive here intelx.io/?s=*&b=web.public.kp&pb=1) the above picture caught our attention. There are many of .KP domains that are unknown to us and everyone else.
What does the above picture actually show? It lists the top “20 North Korean domains” based on average bandwidth, as collected on upstream internet points in (!) the US (specifically at least from AT&T). It essentially lists traffic from people within the US to North Korean domains.
It does not take long to realize that most of the listed KP domains are complete garbage. For example, “zfr8.kp” cannot be resolved in DNS and by simply looking at the domain name itself, it would not make much sense. The full .KP TLD zone was accidentally made available for transfer on September 19, 2016; it’s always possible to look up the full list of KP domains here – github.com/mandatoryprogrammer/NorthKoreaDNSLeak – without relying on live DNS lookups.
Below are all domains listed from the picture with additional information provided by us. 12 out of 20 domains are invalid/fake: that’s 60% of domains shown in the presentation slide.
| NSA listed .kp domains | Bandwidth Kbps | Intelligence X Info |
|---|---|---|
| star-co.net.kp | 609 | Real domain, main NK email provider (no website) |
| silibank.net.kp | 131 | Real domain, used for emails (no website) |
| star.edu.kp | 2 | Real domain, used for emails (no website) |
| water.ocn.ne.kp | < 1 | Non-existent |
| star-di.net.kp | < 1 | Real domain, used for emails, likely only historically |
| aimlessnessm.kp | < 1 | Non-existent |
| vok.rep.kp | < 1 | Real domain, Voice of Korea |
| zfr8.kp | < 1 | Non-existent |
| xmufi.kp | < 1 | Non-existent |
| zeido.kp | < 1 | Non-existent |
| kpnwoa.mts.kp | < 1 | Non-existent |
| azzoz.kp | < 1 | Non-existent |
| fuana.kp | < 1 | Non-existent |
| naenara.com.kp | < 1 | Real domain, Korea Computer Center |
| rodong.rep.kp | < 1 | Real domain, Rodong Sinmun, daily newspaper |
| kcna.kp | < 1 | Real domain, Korean Central News Agency |
| majucm.kp | < 1 | Non-existent |
| ziij.kp | < 1 | Non-existent |
| poqoce.kp | < 1 | Non-existent |
| netmwa.kp | < 1 | Non-existent |
How is the NSA intercepting emails sent to North Korea?
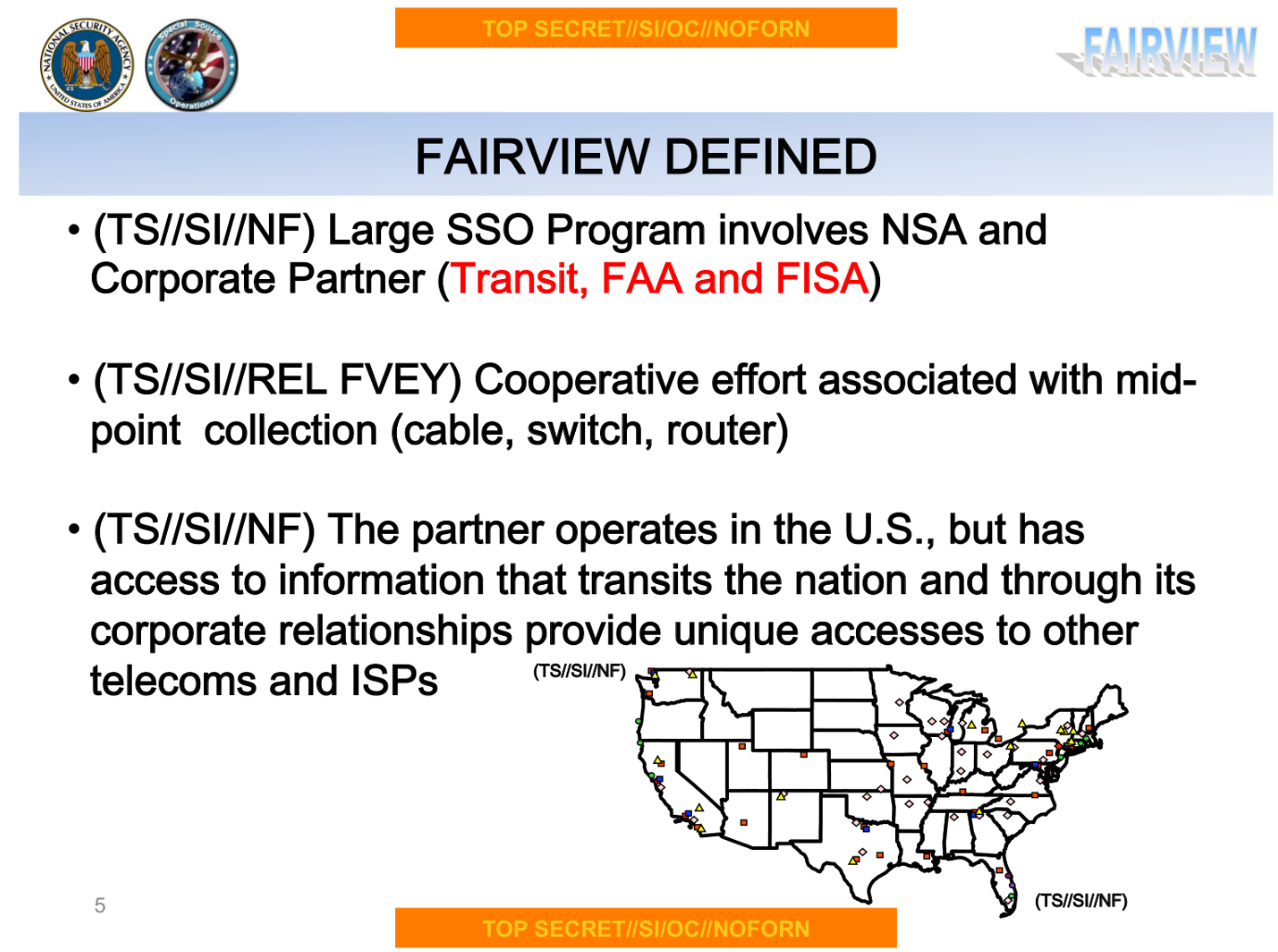
NSA intercepts traffic with Fairview via “cooperative effort associated with mid-point collection (cable, switch, router)” [3] slide 5. NSA is also tapping cables according to slide 4. Whatever traffic – whether garbage or not – comes through those access points and gets sniffed by NSA.

The presentation lists “DNI: Port 25” on slide 9 (DNI = “Digital Network Intelligence”). In human-speak this means sniffing port 25, which is used for SMTP (the protocol for sending emails). Since the North Korean SMTP servers do NOT support SSL, they are sent in plain text over the wire.
All of this means that essentially any email sent in the United States to a .KP (North Korea) domain will be intercepted by the NSA.
How are these false positive .KP domains produced and intercepted by NSA?
As mentioned NSA will sniff everything, whether garbage or not. One of the mentioned domains, “water.ocn.ne.kp”, quickly reveals the source of the false positives. It is a combination of spam and typos. There are actual email addresses that exist for the domain “water.ocn.ne.jp” (note the ending .JP for Japan, instead of .KP). The site, file.scirp.org/Html/7-1780056_25523.htm, lists the email “myhp.na@water.ocn.ne.jp” and is dated to 2012, matching the year of the presentation.
This particular non-existent “water.ocn.ne.kp” domain likely ended up in the NSA slide because somebody made a typo at the end of the email address, sending it to .KP, rather than .JP. It shows how is easy it is, simply making a typo mistake while sending an email, to end up forever in the NSA collection.
At the same time, it is surprising how little false-positive detection and quality control is done. North Korea is a high-value target and listing 60% non-existent domains (falsely associating them with North Korea) on a slide is an intelligence failure.
North Koreas Actual Domains
Here is a full list of actual .KP domains (source: Intelligence X). We are aware of a few more domains that are not publicly known. We may release them later this year.
| Domain | Title |
|---|---|
| airkoryo.com.kp | National airline: Air Koryo |
| www.airkoryo.com.kp | National airline: Air Koryo |
| cooks.org.kp | Korean Association of Cooks: North Korean recipes |
| www.cooks.org.kp | Korean Association of Cooks: North Korean recipes |
| dprkportal.kp | DPRK Portal |
| www.dprkportal.kp | DPRK Portal |
| fia.law.kp | Financial Intelligence Agency |
| friend.com.kp | Committee for Cultural Relations / Korean Friendship Association |
| www.friend.com.kp | Committee for Cultural Relations |
| gnu.rep.kp | Pyongyang Broadcasting Service, radio station |
| www.gnu.rep.kp | Pyongyang Broadcasting Service, radio station |
| gpsh.edu.kp | Grand People’s Study House |
| www.gpsh.edu.kp | Grand People’s Study House |
| kass.org.kp | Korea Association of Social Studies |
| www.kass.org.kp | Korea Association of Social Studies |
| kcna.kp | Korean Central News Agency |
| www.kcna.kp | Korean Central News Agency |
| kftrade.com.kp | Foreign Trade of DPR of Korea |
| www.kftrade.com.kp | Foreign Trade of DPR of Korea |
| kiyctc.com.kp | Korea International Youth and Childrens Travel Co. |
| knic.com.kp | Korea National Insurance Co. |
| korean-books.com.kp | Korean Books |
| www.korean-books.com.kp | Korean Books |
| koredufund.org.kp | Korea Education Fund |
| www.koredufund.org.kp | Korea Education Fund |
| korelcfund.org.kp | Korea Elderly Care Fund |
| www.korelcfund.org.kp | Korea Elderly Care Fund |
| korfilm.com.kp | Korea Film Corporation: North Korean movies |
| kut.edu.kp | Kim Chaek University of Technology |
| www.kut.edu.kp | Kim Chaek University of Technology |
| ma.gov.kp | Martime Agency |
| www.ma.gov.kp | Martime Agency |
| mail.silibank.net.kp | International email service |
| manmulsang.com.kp | Manmulsang Commerce Website |
| mediaryugyong.com.kp | Ryugyong Programming Center |
| mfa.gov.kp | Ministry of Foreign Affairs |
| www.mfa.gov.kp | Ministry of Foreign Affairs |
| mirae.aca.kp | Mirae |
| www.mirae.aca.kp | Mirae |
| naenara.com.kp | Korea Computer Centre |
| www.naenara.com.kp | Korea Computer Centre |
| pulbora.edu.kp | Samhung Intellectual Assets Center |
| www.pulbora.edu.kp | Samhung Intellectual Assets Center |
| pyongyangtimes.com.kp | The Pyongyang Times |
| www.pyongyangtimes.com.kp | The Pyongyang Times |
| rodong.rep.kp | Rodong Sinmun, daily newspaper |
| www.rodong.rep.kp | Rodong Sinmun, daily newspaper |
| ryongnamsan.edu.kp | Kim Il Sung University |
| www.ryongnamsan.edu.kp | Kim Il Sung University |
| sdprk.org.kp | Sports in the DPRK |
| www.sdprk.org.kp | Sports in the DPRK |
| smtp.star-co.net.kp | ISP-related |
| smtp.star-di.net.kp | ISP-related |
| tourismdprk.gov.kp | National Tourism Administration |
| www.tourismdprk.gov.kp | National Tourism Administration |
| vok.rep.kp | Voice of Korea |
| www.vok.rep.kp | Voice of Korea |
| youth.rep.kp | Information on Korean Youth |
| www.youth.rep.kp | Information on Korean Youth |
References
[1]
propublica.org/article/nsa-spying-relies-on-atts-extreme-willingness-to-help
[2]
electrospaces.blogspot.com/2015/08/fairview-collecting-foreign.html
electrospaces.blogspot.com/2014/01/slides-about-nsas-upstream-collection.html electrospaces.blogspot.com/2014/01/slides-about-nsas-upstream-collection.html
[3]
documentcloud.org/documents/2274319-fairviews2dbriefings11march2013.html