I2P added to the index 👀
We have now added another darknet to our index: I2P. It is substantially smaller in terms of hosted sites than its bigger fellow, Tor. To connect via I2P, you’d normally have to download the I2P router which provides an HTTP proxy in order to visit “.i2p” domains (called “eepsites”) from the browser. The I2P software is unfortunately written in Java – a big no-no when it comes to security (and also performance).
To search only within the I2P darknet on Intelligence X, select “Darknet: I2P” in the Advanced menu:
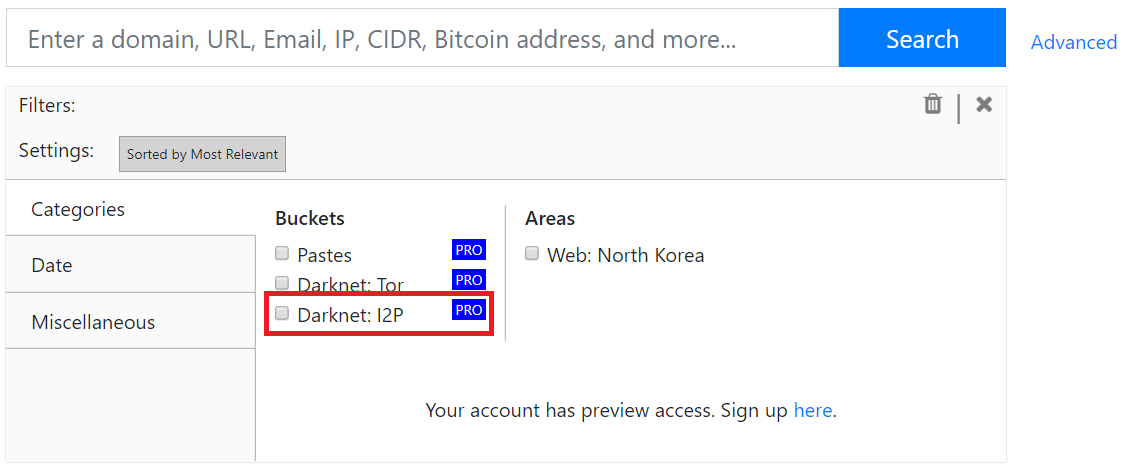
To view the latest I2P indexed content, click on this link: intelx.io/?s=*&b=darknet.i2p&so=4
Why is this useful?
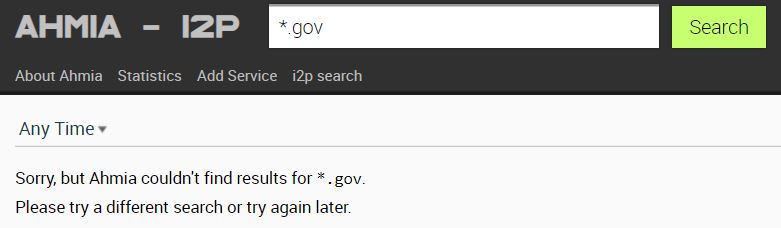
There are not many existing search engines for Tor or I2P. One of them is Ahmia.fi, however no matter what search terms we used, we ended up with no results:
When using Intelligence X you’ll immediately find content that matches your query:
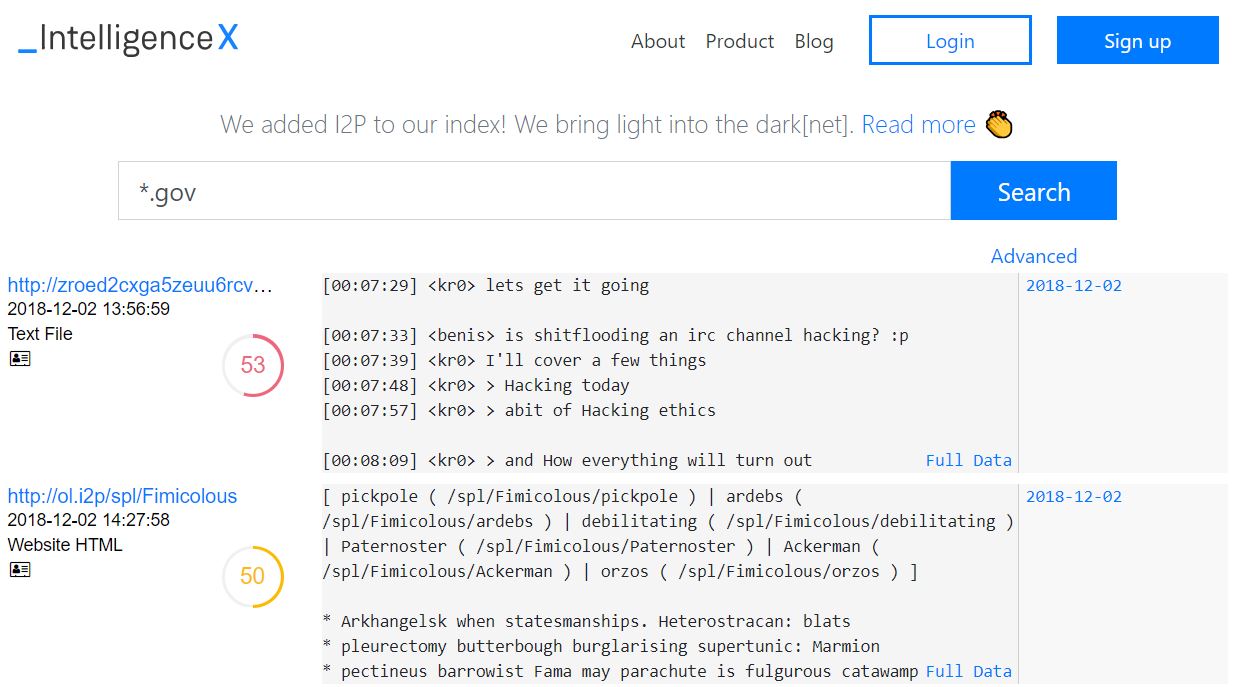
The first benefit of making I2P sites searchable is simply discovery; the second is archiving I2P sites long-term.
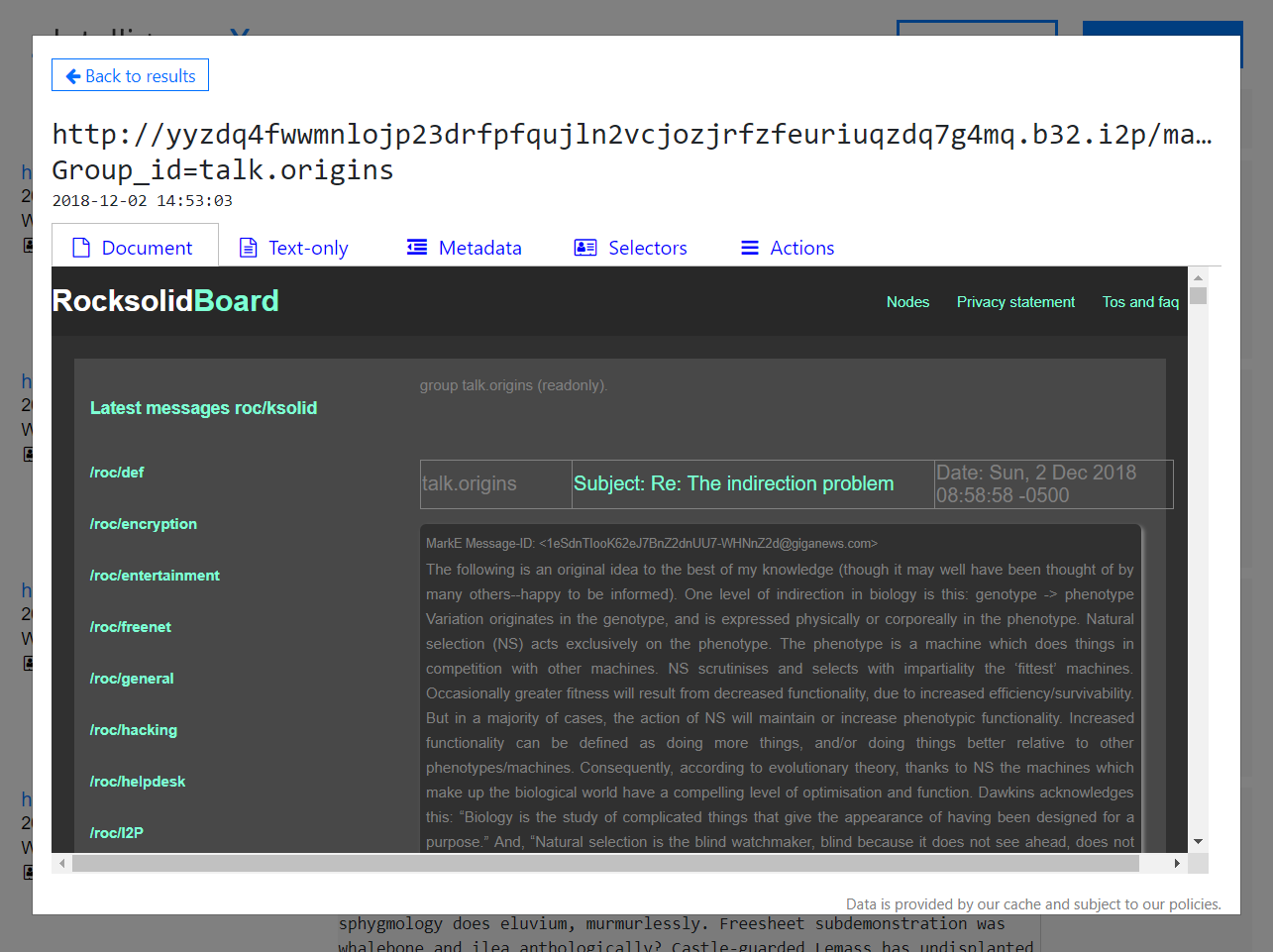
As mentioned, you either have to download the I2P router and run it locally, or use an I2P web proxy in order to access “.i2p” websites. Upon opening the detailed view in Intelligence X for a result (by clicking in the result’s title, or on “Full data”), you can immediately see how the original website looks like. Any dangerous HTML tags (and others) are removed, so it is always safe to view.